Author – Zaid Qureshi
Security is included in the services of AWS in accordance with security best practices, and documents how to use the security features. Ensuring the confidentiality, integrity, and availability of user’s data is of the utmost importance to AWS, as is maintaining their trust and confidence.
A glance at security in the AWS Cloud:

Certifications and accreditations: To gain trust and prove it’s security, AWS has successfully completed multiple audits, AWS has achieved ISO 27001 certification, and has been validated as a Level 1 service provider under the PCIDSS and now publishes a Service Organization Controls 1 report.
Physical security: Knowledge of the location of the data centers is limited to those within Amazon who have a legitimate business reasons for this information. These locations are secured physically in a wide variety of ways to stop any malicious activity.
Secure services: Each service in AWS is designed to be secure. These services are created in such a way so that it can block the unauthorized access.
Data privacy: Private and business data can be encrypted by the users in the AWS cloud, and their customers can protect their by using the data published for backup and redundancy procedures for services and keep their applications running.
Security Challenges in the Cloud:

The cloud computing service has various privacy and security concerns:
Outsourcing: Users may lose control of their data. Appropriate mechanisms needed to prevent cloud providers from using customers data in a way that has not been agreed upon in the past.
Extensibility and Shared Responsibility: There is a trade-of between extensibility and security responsibility for customers in different delivery models.
Virtualization: There needs to be mechanisms to ensure strong isolation, mediated sharing and communication between virtual machines.
Multi-tenancy: There are a lot of risks in sharing the resources with others, especially when sensitive data is being stored in the cloud, as many clients can share the same resource, privacy is a big challenge in cloud.
Everyone is concerned about security in a multi-tenant environment. In every layer of the cloud application architecture security should be implemented. Physical security is of course handled by the service provider, which is an additional benefit of using the cloud. Network and application-level security is user’s responsibility.
eDDoS (economic Distributed Denial of Service):
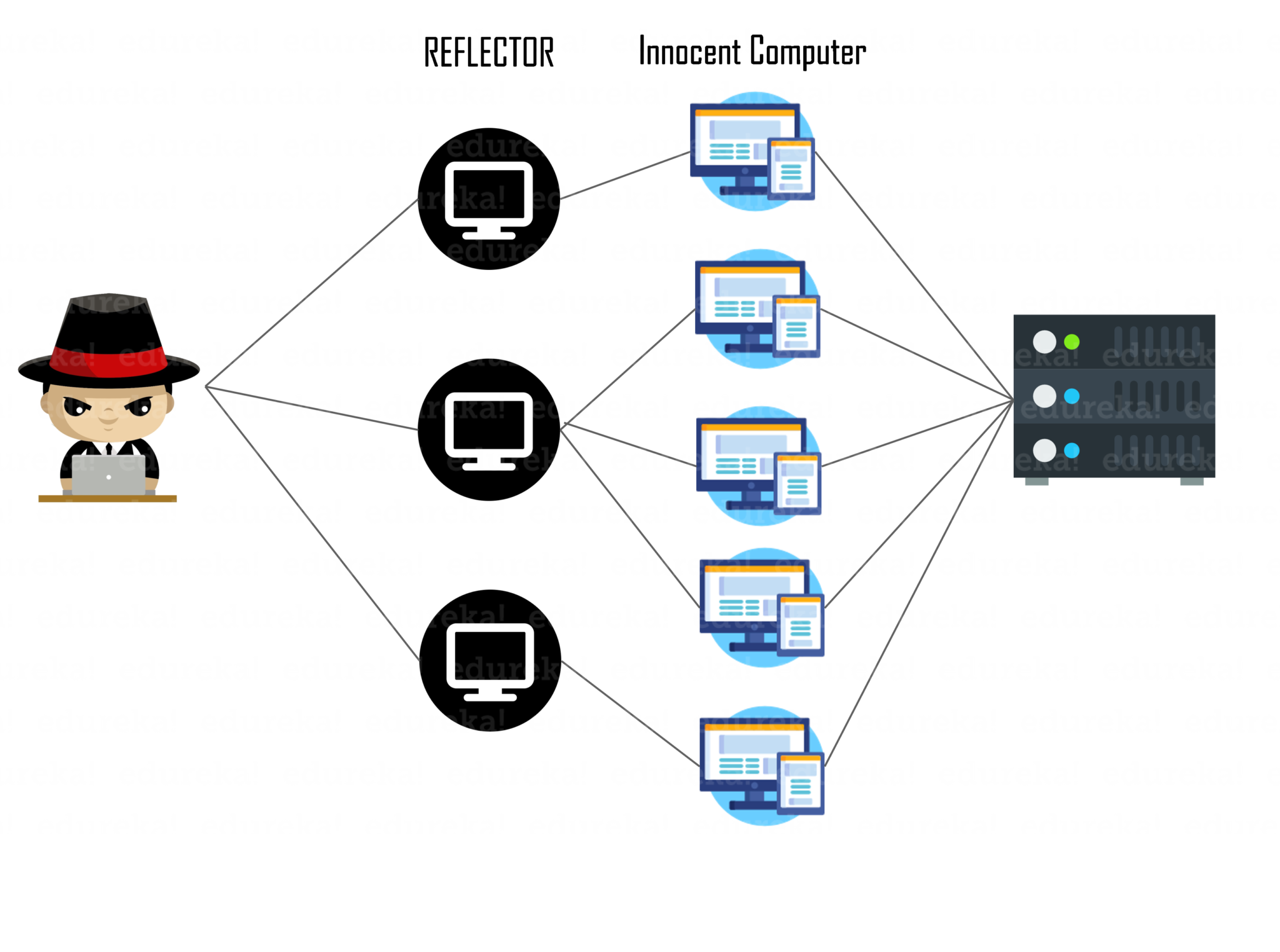
DDoS attacks causes eDDoS in the cloud, in which the availability to the genuine user is never denied. But the service provider who is using cloud will incur a hugely increased bill by using highly elastic capacity to unwillingly serve a large amount of unwanted traffic in order to maintain the availability. Hence it is necessary to drop the DDoS before the billing mechanism starts for the service provider.
Cloud Storage security:

Data storage is one of the most commonly used cloud service, any amount of data end users can be outsourced to cloud servers to enjoy virtually unlimited hardware/software resources and access, with no or little investment.
The data is stored elsewhere. We can not be sure no one can access it. If something affects storage provider, like outages or malware infections, that will directly impact access to your data. The storage is shared between different clients as needed. The data might be at risk if others are using your servers as well.
RESPONSIBILITY FOR CONTROLS IN CLOUD COMPUTING

Cloud computing only transfers the responsibility to perform compute task according to certain parameters, but accountability remains with the Client. The decision of whether the Client or the Provider is responsible for a given control depends on these factors:
- The cloud model (SaaS, IaaS, or PaaS) chosen.
- The extent to which the Client is allowed to configure the Provider’s controls.
Client is always responsible for securing the computing resources it retains. All other security controls become void if the Client fails to deploy controls to protect the servers, notebooks, and networks that it uses to access the Provider. It is entirely the Client’s responsibility to implement suitable controls to prevent client-side threats such as the web browser vulnerabilities, theft of authentication credentials, virus attacks, or data theft by rogue employees.

SaaS cloud models.
Consequently, we obtain the following responsibilities:
• In all three cloud models, the Provider is responsible to implement and operate suitable infrastructure controls such as employee training, physical site security, network firewalls, and others. Infrastructure controls are of fundamental importance.
• In IaaS, the Client manages and controls all software that runs on the Provider’s infrastructure. As such, the Client is responsible for all software security controls, including software patching, anti-virus protection, application access control, user identity management, and others.
• In PaaS, the Client manages and controls the application software, while the Provider manages the OS, infrastructure, middleware. The Client is responsible for all app controls, while the Provider is responsible for the IT general controls .
• In SaaS, the Provider manages and controls all layers of the software stack and is accordingly responsible for their security. In other words SaaS providers are responsible for implementing suitable security controls in their infrastructure, operating systems and middleware, as well as application software.
Conclusion:
Cloud has its own benefits and provides security, but along with it comes the risks and challenges of using cloud. By understanding the proper documentation of the Cloud Providers and using the security best practices, one can protect his/her data in the cloud with proper security configurations and management. Cloud Providers and Clients have different controls over the cloud in different cloud models, and they should be well aware of their controls, and responsibilities to securely run their respective organizations.
References:
“https://ieeexplore.ieee.org/document/6427581”
“https://www.sciencedirect.com/science/article/pii/S1877050914010187”
“https://www.researchgate.net/publication/340295800_Cybersecurity_in_the_AWS_Cloud”