Author – Zaid Qureshi
Although you may not have heard about them recently, distributed denial of service (DDoS) attacks have increased in frequency and size with the internet’s growth. Fortunately, our options for dealing with these threats have grown as well. One of the greatest approaches uses the Cloud’s natural distributed nature to defend servers against malicious traffic all across the world. Cloud DDoS Protection or Cloud Anti-DDoS is the term for this.
What is DDoS Attack?
A DDoS attack happens when a dispersed network of devices delivers an enormous volume of fraudulent data to a target server or network, thereby denying service by crowding out genuine users trying to access the site during the attack. These hostile networked devices are generally either purpose-built servers dedicated to the assault (if the attacker has financial resources) or a “botnet,” which is a collection of malicious networked machines (a network of bots).
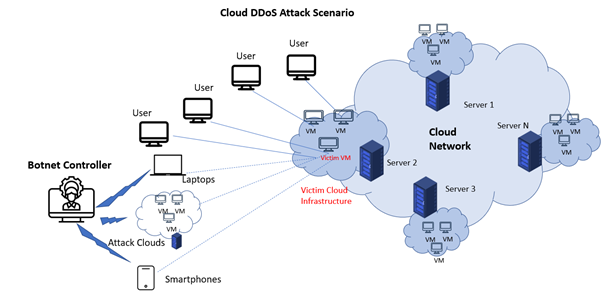
In virtualized multi-tenant systems, an infrastructure cloud often contains many servers ready to handle virtual machines. Attackers may target economic sustainability criteria of cloud users while launching a cloud DDoS assault. This assault has been dubbed the FRC (Fraudulent Resource Consumption) attack after a few other contributors. DDoS assaults are used to plant trojans and bots on weak workstations across the target web services and the Internet.
Botnets are made up of infected equipment, including internet-connected home gadgets. Some of these “bots” include computers, laptops, and servers, but the bulk are things you may not expect, such as a home-networked security camera system or a refrigerator. Malicious malware may even be embedded in online adverts, leading your phone to be attacked while you are playing an ad-supported game. Attacking machines may be found almost anywhere, and they all work together to eliminate the victim.
Protection in Cloud:
You need a worldwide network to defend yourself since the botnet has a global network. This is where Cloud DDoS Protection (also known as Cloud Anti-DDoS) comes into play. Attacking traffic is cleaned near the source, not at the destination, using numerous global scrubbing centres. The attacker traffic never even makes it close to your server.
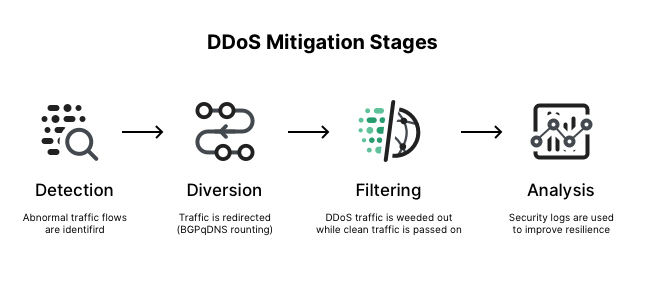
You don’t need an army of thousands, unlike the botnet. Scrubbing should be handled by a few focused, high-bandwidth nodes. Otherwise, our traffic will become backed up and sluggish. The trick is to strike the correct balance between preventing attacks and allowing legitimate traffic to flow without interruption.
This technique not only allows for scalability, but it also avoids the remainder of the network from being crowded during an attack by cleaning the data near the source.
A cloud DDoS solution can automatically build protection for zero-day and unknown DDoS attacks in real-time within seconds, thanks to behavioural-based detection and real-time signature development technology.
DDoS protects across the network and application levels, including volumetric and non-volumetric attacks, as well as full coverage of SSL-based DDoS attacks.
Some features of Cloud DDoS Protection are:
Adaptive security: With an ML system trained locally on our apps, we can automatically detect and help prevent high-volume DDoS attacks.
Hybrid and multicloud installations are supported: Whether our application is installed on Cloud or in a hybrid or multicloud architecture, we can help protect it from DDoS or web assaults by enforcing security standards.
Pre-configured WAF rules: Pre-configured WAF rules are out-of-the-box rules based on industry standards that assist guard against common web-application vulnerabilities and the OWASP Top 10.
Bot administration: Through native integration with reCAPTCHA Enterprise, provides automatic bot protection for our apps and helps combat fraud in line and at the edge.
Limiting the rate of change: Rate-based restrictions safeguard our apps from excessive volumes of requests that overwhelm our instances and prevent genuine users from accessing them.
Access control based on IP address and location: Filter inbound traffic using IPv4 and IPv6 addresses, as well as CIDRs. Determine and enforce access controls based on incoming traffic’s geographic location.
Attacks in the Future:
In the future, DDoS-for-hire services will be the future of DDoS attacks, with cloud infrastructures and Internet of Things devices becoming important attack sources and targets.
Knowledge of scalability, resource pricing, other details, and users’ behaviour may be used in volumetric but smart assaults.
Both sides are viewed as armies, with the winning army often having greater resources. However, when it comes to DDoS assaults in cloud computing, we’re seeing a distinct pattern.
In this case, the victorious side may not be the one who spends the most on resource acquisition.
References:
[1] Ishtiaq Ahmed, Sheeraz Ahmed, Asif Nawaz, Sadeeq Jan, Zeeshan Najam, Muneeb Saadat, Rehan Ali Khan and Khalid Zaman, “Towards Securing Cloud Computing from DDOS Attacks” International Journal of Advanced Computer Science and Applications(IJACSA), 11(8), 2020.
[2] G. Somani, M. S. Gaur, D. Sanghi, M. Conti, M. Rajarajan and R. Buyya, “Combating DDoS Attacks in the Cloud: Requirements, Trends, and Future Directions,” in IEEE Cloud Computing, vol. 4, no. 1, pp. 22-32, Jan.-Feb. 2017, doi: 10.1109/MCC.2017.14.